DeadEye is a software that will attempt to trick the users into using this unwanted application as the utility to incread the performance of the computer. DeadEye will run if a presence of Java Runtime Environment is present on victims computer, if not, it will attempt to download JRE.EXE file from�its own server.�
Robert La Nguyen
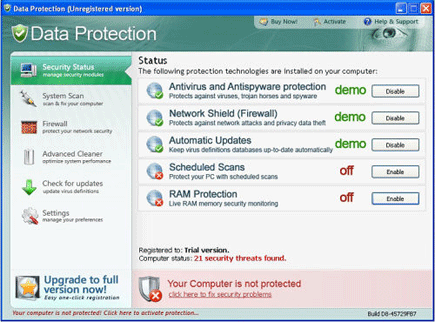
Remove Data Protection Virus
Data Protection is another piece of rogue security software that will pretend as anti-virus application. This unwanted program can be dropped on computers without users knowledge when executing prompts from a fake online virus scanner web sites. Data Protection malware will alter system settings and add its own value on the registry so that it will run when Windows is started. Changes will be made to installed Internet browser so that it will redirect to various malicious websites when a searched was made.
Remove Antispyware Soft
Antispyware Soft is another malicious security application that will display excessive fake alerts on victim’s computer. Antispyware Soft virus will spread by means of Trojan that are able to alter system settings specially Internet browser and redirects its homepage and search result page to a fake online virus scanner. This web page will perform a scan on visitor’s computer and produce fabricated results about potential virus infection on the computer. It will advise to download and install Antispyware Soft to clean and remove detected threats.
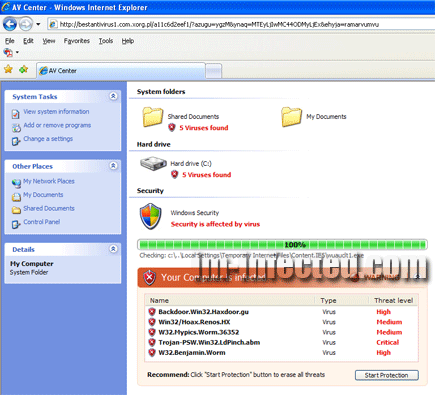
Remove AV Center
AV Center is a rogue security program that requires immediate removal from infected computer. AV Center Trojan is capable of updating itself by downloading more files from a remote server. Common ways to get infected with AV Center is for user follows a prompt that will redirect Internet browser to a fake online virus scanner. This scanner will mimic Windows explorer as if it is performing the virus scan on the computer locally.
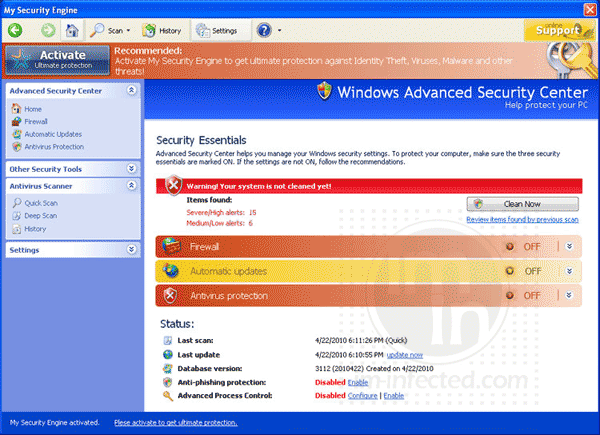
Remove My Security Engine
My Security Engine is another misleading security application that will attack a computer by pretending to be a useful program. Just like any other rogue software, this threat will use deceiving data posted on computer screen to persuade users into downloading and installing the trial of the software. Upon installation, it attempts to modify certain settings on the system and add some registry entries.
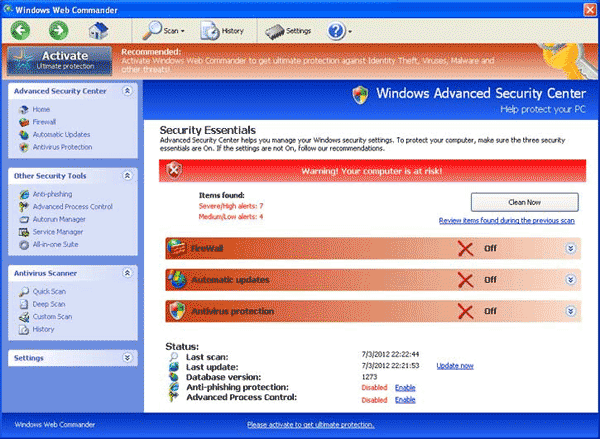
Remove Control Commander
Control Commander with alias CtrlCommander is a misleading security tool for Windows that was created to look and perform like a real antivirus program. However, security experts deemed the tool as harmful and therefore it was categorized as rogue or fake security software.
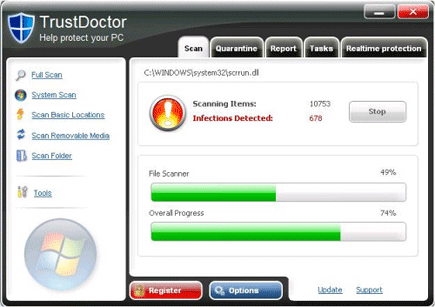
Remove Trust Doctor
Trust Doctor and sometimes called as TrustDoctor virus will invade a computer without being noticed by the user. It can be installed through software vulnerabilities that were exploited by a Trojan. Spam emails and malicious links you may receive on social networking sites and instant messenger can also lead to the virus infection.
Remove Vista Security Tool 2010
Vista Security Tool 2010 is misleading computer anti-virus software. It is known also as rogue program. This type of threat is designed to earn a profit for its developer for planned fraudulent online activities. Vista Security Tool 2010 may sneak into computers via Trojan that will successfully download and install it without being detected by your anti-virus software.
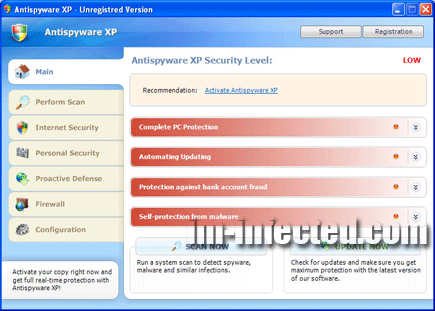
Remove Antispyware XP
Antispyware XP is a rogue anti-virus program that usually spreads by means of a Trojan infection. The Trojan can manipulate an infected computer so that it will redirect to a website where users will acquire Antispyware XP without their knowledge. Computers infected with this virus will have difficulty in browsing the Internet because it will hijack web pages and instead display a fake warning page. A continuous warning and task bar messages will be exhibited by Antispyware XP to scare users about presence of viruses on the PC.
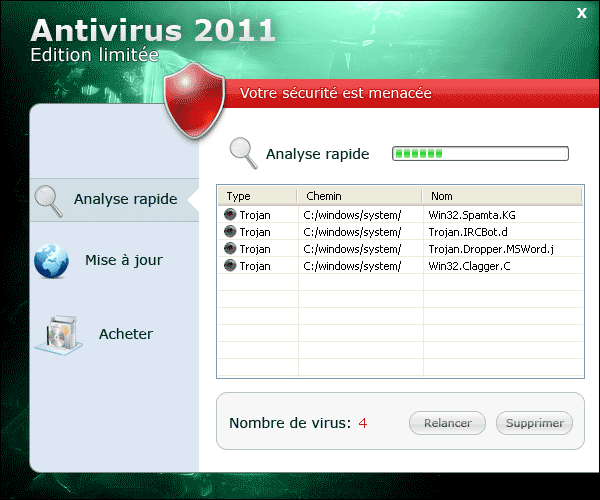
Remove Anti-Virus 2011
Anti-Virus 2011 is a malware that came from the same author who perpetuated other malicious software such as Antivirus Soft. These rogue programs may enter the computer with the help of a Trojan created to take advantage of un-patched security loopholes from an Internet browsers and Flash applets. Fake Java update is another source that you may look into. It can disguise as valid installation file of Java.