If your browser is automatically redirecting you to the unknown, irrelevant pages without your permission, it might be because of a Browser Hijacker malware.
Read this post further to know all about Browser Hijacker. How it enters your device, what its symptoms are, how to remove hijackers from the browser, and some preventive measures.
What is Browser Hijacker?
A Browser Hijacker is one of the types of malware program that maliciously takes control of your browser and overrides its settings to conduct illicit activities like unintentional redirection, ad bombardment, irrelevant pop-ups, malicious downloads, and more. Some advanced hijackers are designed to fill the device with unnecessary junk and cause system failure.
There are even some cases in which Browser Hijacker was responsible for the Ransomware attacks. However, most commonly, Browser Hijackers are utilized by online attackers and fake website owners to increase the number of visitors on their websites and generate ad revenues.
Why is Browser Hijacker dangerous?
To many users, the Browser Hijacker might just be an annoying malware disturbing their browsing experience. However, a hijacker can be much more devastating than just being irritating. Here are the top reasons why a Browser Hijacker can be dangerous for your computer:
- After taking control of your browser, a Browser Hijacker can conduct various malicious acts. It can initiate an unintended download of malware programs or codes.
- A hijacker can collect your browsing data, such as search history, cookies, IP address, and more. The cybercriminals behind the hijacker can illegally sell this accumulated data to advertisers or marketing agencies, thereby putting your privacy in danger.
- A Bowser Hijacker malware can act as a gateway for other dangerous malware like Trojans, Spyware, Ransomware, and others. These malware programs can steal valuable data such as banking details or encrypt your data and ask for ransom in return for decrypting tools or keys.
- Since browser settings are in control of the hijacker, the user can be forcefully redirected to the malicious pages and infect their computers.
- The hijacker can install malicious plugins and ruin your browsing experience.
- Some pop-ups or extensions installed by the hijacker can download malicious apps through drive-by-downloads. It does not even require human intervention like clicking.
How does a Browser Hijacker enter my system?
Web browser hijackers might get into the system in many ways. Most of the time, it happens due to the user’s carelessness or lack of awareness. Here are the top ways through which a Browser Hijacker infiltrate your system:
Bundled Software
When you install a new program on your system, many of them might come with an added program that you didn’t intend to install. Many users in the hurry of installing the software ignore the bundled program, and it also gets installed along with the primary program in the system. Such additional programs can introduce the browser hijacker in your system.
Clicking on Malicious Pop-ups
Pop-ups are a good feature for genuine websites to interact with their visitors. However, cybercriminals are exploiting this amazing tool to conduct malicious activities. Many online attackers are using pop-ups to introduce malware programs in the user’s device who clicks them. For this, they design pop-ups with fake offers and intriguing headlines to lure internet users into clicking. Clicking on such infected pop-ups might redirect users to illicit websites or trigger the installation of malware programs like Browser Hijacker, Adware, Trojans, and others.
Downloading from Third-Party Sources
In anticipation of getting paid software for free or at a lower price, many users take the route of third-party sources. Most of these third-party sources are pirated and filled with fake and infected programs that appear legitimate. In greed, many users ignore the dangers of such infected software and download & install them on their machines. After getting installed, the malicious software program can introduce Browser Hijacker and other malware to the system.
How does a Browser Hijacker work?
Most Browser Hijackers are used only for the purpose of gaining ad revenue by redirecting users to specific pages or search engines. After getting into your system through the ways mentioned in the previous section, Browser Hijacker begins its working. It will target your browsers and take control of their settings. Once the settings are hijacked, it is easy to make changes like changing the default search engine, default homepage, new tab redirects, and more. Even if you restore these settings, the hijacker will change it again, and it will keep happening until the hijacker responsible for it is deleted.
Symptoms of Browser Hijacker infection
When the malicious Browser Hijacker enters your system, you will notice some unusual changes that automatically indicate the virus’s presence. Here is the list of some indications that confirm the infiltration of the Browser Hijackers:
- You will notice unknown Browser on the desktop that got installed automatically.
- The default web browser is changed to a fake browser installed by the hijacker.
- There is some illegitimate search engine or a webpage set as the default.
- You will notice a lot of advertisements while browsing the internet.
- The system becomes slow and sluggish because of continuous redirection and ad bombardment.
- The other browser you are using is hijacked, and settings are modified to promote fake search engines and web pages.
- You might even see some unknown applications get automatically installed on your system.
How to remove Browser Hijacker?
Browser Hijackers get installed like any other applications on your system or extension on the browser; however, completely removing them from the system is challenging. Even if you uninstall the culprit applications or extensions, the traces would still remain.
To remove the Browser Hijackers entirely from the system, follow these measures:
Reboot your system in Safe Mode
Whenever you suspect a Browser Hijacker attack or any other malware attack on your PC, the first thing you should do is restart your computer in the Safe Mode. It is because, in normal mode, your device might not be functioning correctly due to the presence of the hijacker. The Safe Mode disables every application, excluding the essentials one. This way, you can easily track the culprit application and uninstall it while being on Safe Mode.
Uninstall Suspicious Applications
If you are not in Safe Mode, you can still catch the malicious programs and uninstall them. To do that, follow these steps:
-
Right-click on the Windows taskbar and select Task Manager.
-
On the Task Manager window, look for the applications or processes that you don’t remember installing.
-
Right-click on such programs and choose Open file location.
-
Delete all the files related to the applications from the root location.
-
Deleting the files is not enough. You have to uninstall the applications too. For that, navigate to the Control Panel.
-
Choose Uninstall a program.
-
Right-click on the suspicious applications and select Uninstall.
Remove Malicious Web Extensions from Browser
Web Extensions are pretty helpful in making browsing easier and make the most use of the browser’s capabilities. Google Chrome’s web extensions are pretty popular among users. Taking advantage of this, cyber attackers release malicious Browser Hijackers and other malware in the name of legitimate extensions or add-ons.
To check the list of installed web extensions and remove the suspicious ones on Google Chrome, follow these steps:
- Launch Google Chrome Browser and click on the three dots at the top right corner. Hover your mouse to More tools and select Extensions.
- You will see the list of all your installed web extensions.
- Look for the suspicious ones that you don’t remember installing and remove them. You can also disable them if you are unsure whether they are malicious.
Reset Browser Settings
After getting rid of the application or extension responsible for the hijacking, it is time to reset the browser’s settings to default.
Follow these steps to reset browser settings in Google Chrome:
- Launch Chrome, click the three-dots at the top-right corner, and select Settings.
- On the settings page, scroll down and click on Advanced to open advanced settings.
- Next, on the Advanced settings page, navigate to the Reset and cleanup section and click on Restore settings to their original default.
- On the following dialog box, click on the Reset settings button.
Scan your device with an Antimalware
Manually finding the malicious application and then removing it and its components from the system might be tedious for many users. If you are one of them then you can use robust security applications like antimalware programs that would detect malicious programs or files and remove them from the system.
How to prevent Browser Hijacking?
Till now, you might have known how dangerous Browser Hijacker can be. It is better to prevent such malware attacks on the device rather than dealing with them after the infection.
Here are some preventive measures to keep your device away from Browser Hijacker programs:
Use robust Security Program
Getting a robust dedicated security program for your machine would ensure a tight security layer between malware programs and computers. Security applications like antimalware or antivirus are specifically designed to detect malicious codes or programs and prevent their infection. If you try to navigate to an infected link or download a suspicious file, the security program might prevent those from happening, thereby eliminating the chance of any malware attack.
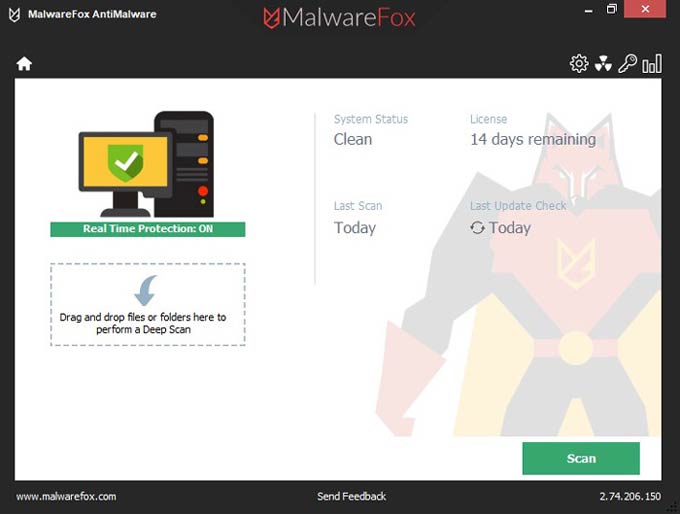
If you are confused about which security program to go for, we have an excellent suggestion for you. MalwareFox is reliable security software that promises to protect your system and helps to handle malware and viruses. MalwareFox will scans, detect, and remove Malware and offers real-time protection It also protects your PC from the most dangerous malware such as Ransomware, Zero-Day Attack protection, Grayware, Keyloggers, etc.
Avoid Downloading Software from Unknown Sources
Malicious software programs are one of the most common malware carriers. Users must avoid getting any software programs from unknown third-party sources in greed of getting them for free or at a lower price. This should be avoided at any cost as software downloaded from third-party sources can be infected with malware.
Keep your OS and Apps Updated
Updating the operating system will not only introduce the new features but also update the system with the latest security patch. The computer with the updated security patch will be able to tackle the new Browser Hijacker programs and other latest malware more conveniently. Similarly, it is also advised to keep all the installed applications updated with the newest version. An outdated application might open the door for malware entry because of its outdated security. Updating the applications will fix the security vulnerabilities and reduce the chances of malware attacks.
Use Secured Network
Many users like to connect to the unsecured public Wi-Fis as most of them are free to use. However, people are not aware that these public Wi-Fis are highly unsecured. Any intruder can easily hijack the user session on such networks and conduct illicit activities like introducing Browser Hijackers and other malware. It is advised never to connect to public Wi-Fi networks. If you have any urgency, use a robust VPN service and don’t share any sensitive details while connected to unknown networks.
Practice Safe Browsing
The internet has revolutionized everyone’s life with its lots of advantages. However, people need to know that not everything on the internet is good. While browsing, you will find many illicit websites that might tempt you to visit them. Likewise, you will also find intriguing pop-up and banner ads that would offer you “too good to be true” offers. It would be best to always ignore such websites and ads as they are one of the primary sources of malware spread. Always practice safe browsing to eliminate any risk of Browser Hijacker and other malware attacks.
Keep yourself Informed
Knowledge about Browser Hijackers, how they spread, and their attacking methods will always help you stay protected and even inform and save others from such devastating malware. It is advised to regularly read about the latest happenings in the cybersecurity world and what new hijackers are emerging.











