Creeper ransomware is a computer virus that encrypts various files stored on bug machine. Then malware author requires victims to pay in Monero cryptocurrency to recover their data. This dreadful threat will lock access to your databases, images, videos, and other files you treasure. You may easily notice which files are encrypted, as it renames by adding .creeper extension.
Cyber crook tries to force victims to pay immediately. It declares that the amount of ransom will be based on how fast you pay the demand. If you send payment within 2 days, the ransom is 3 Monero coins. If you choose to pay the ransom on the third day up to fifth day, the amount you have to pay will be 5 Monero coins. On the sixth day, you have no more chance to retrieve your files since decryption key will be deleted permanently. Attacker assures victims that all necessary key will be given to you once you settle the ransom.
We have to warn you that people behind this scheme should not be trusted in the first place. Threatening words coming from attacker should be ignored, as well as assurance that they will release your files after paying. The only goal of Creeper virus is to collect money from PC users. Therefore, as long as there are victims who trying to deal with cyber crook, malware author will persuade to develop more ransom virus like this.
It is important to note that Creeper and most ransom virus including TBlocker, Wana Decrypt0r, and Saturn are typically distributed through malicious email attachment. Thus, if you do not know the source, better not to open it. More so, always install program from official web page or trusted free download site to prevent obtaining the same kind of threat.
Meanwhile, the best solution to this computer issue is to get rid of Creeper ransomware. Then scan your computer using advanced and reliable anti-virus program which is capable to detect and remove types of threats. For the time being, you have to depend from your backup to retrieve your encrypted files.
Threat Summary
| Threat: | Creeper |
| Type: | Ransomware |
| Brief Description: | This ransom virus encrypts selected files on the computer and prompts user to pay for decryption key. |
| Protection Tool: | ▼ DOWNLOAD MalwareFox |
Description
Creeper ransomware is a computer virus that encrypts various files stored on bug machine. Then malware author requires victims to pay in Monero cryptocurrency to recover their data. This dreadful threat will lock access to your databases, images, videos, and other files you treasure. You may easily notice which files are encrypted, as it renames by adding .creeper extension.
Cyber crook tries to force victims to pay immediately. It declares that the amount of ransom will be based on how fast you pay the demand. If you send payment within 2 days, the ransom is 3 Monero coins. If you choose to pay the ransom on the third day up to fifth day, the amount you have to pay will be 5 Monero coins. On the sixth day, you have no more chance to retrieve your files since decryption key will be deleted permanently. Attacker assures victims that all necessary key will be given to you once you settle the ransom.
We have to warn you that people behind this scheme should not be trusted in the first place. Threatening words coming from attacker should be ignored, as well as assurance that they will release your files after paying. The only goal of Creeper virus is to collect money from PC users. Therefore, as long as there are victims who trying to deal with cyber crook, malware author will persuade to develop more ransom virus like this.
It is important to note that Creeper and most ransom virus including TBlocker, Wana Decrypt0r, and Saturn are typically distributed through malicious email attachment. Thus, if you do not know the source, better not to open it. More so, always install program from official web page or trusted free download site to prevent obtaining the same kind of threat.
Meanwhile, the best solution to this computer issue is to get rid of Creeper ransomware. Then scan your computer using advanced and reliable anti-virus program which is capable to detect and remove types of threats. For the time being, you have to depend from your backup to retrieve your encrypted files.
Procedures to Remove Creeper
Download FREE Removal Tool
Removal steps on this page will help you get rid of the threat effectively using tools and virus scanners. Please make sure that you will carry out the guide in exact order.
Procedure 1: Scan Computer in Safe Mode Using Installed Anti-virus Program
1. First, we will try to remove Creeper Ransomware Virus (Removal Guide) by running a virus scan under Safe Mode with Networking. To perform this task, please complete these procedures.
Start in Safe Mode with Networking (Windows XP/Vista/7 Instruction)
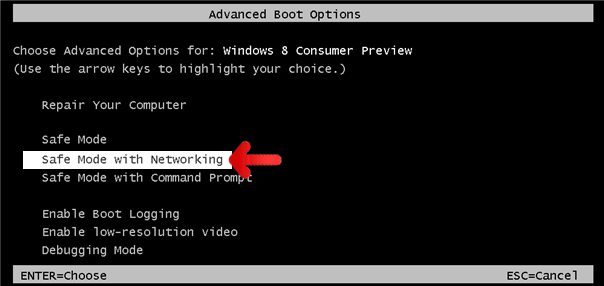
- Please restart the computer and just before Windows start, press F8 on your keyboard repeatedly. You will be presented with Advanced Options Menu.
- From the selections, choose Safe Mode with Networking. Please use keyboard's arrow up/down to navigate between selections and press Enter to proceed.
Start Windows 8 in Safe Mode with Networking
- Please restart the computer and as soon as it begins to start, please press Shift+F8 keys.
- Instead of seeing Advance Boot Options, Windows 8 will display Recovery Mode. Continue with the given steps until you reach Safe Mode function.
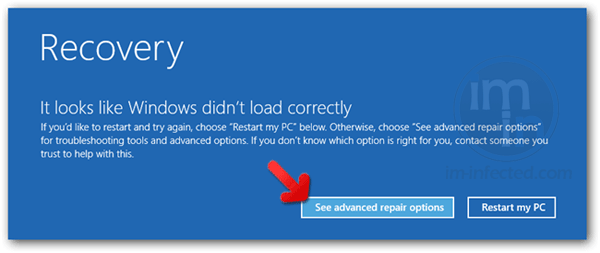
- Click on 'See advanced repair options'.
- Then, click on Troubleshoot.
- Next, please select Advanced options.
- On the next window, please choose Windows Startup Settings.
- Lastly, click on Restart button. Windows 8 will now restart and boot into Advanced Boot Option wherein you can run the system in Safe Mode with Networking.
2. Open your installed anti-virus programs and update it to the most recent version by automatically downloading necessary updates.
3. Thoroughly scan the computer and remove all identified threats. Do not restart or turn off the computer after the scan process. You still need to run another scan. Please follow the next procedure.
Procedure 2: Scan and remove Creeper files with MalwareBytes Anti-Malware
To remove Creeper, download Malwarebytes Anti-Malware. This tool is effective in getting rid of Trojans, viruses and malware.
1. After downloading, please install the program using the default settings.
2. At the end of the installation, please make sure that it will download necessary updates.
3. Once update has completed, MBAM will launch.
4. Select SCAN from the top menu. Then, click on Threat Scan (Recommended) section.
5. Click on Start Scan to thoroughly scan the computer. Remove all threats detected by this anti-malware program after the process.
Procedure 3: Run Microsoft Safety Scanner to remove Creeper components.
MS Safety Scanner is a free security tool that offers on-demand virus scanning and helps remove threats from the infected computer. It is a stand-alone program that works even with existing antivirus program.
Important: Each download of Microsoft Safety Scanner expires 10 days after the acquisition date. If this period lapses, you need to download the same program from the same location again. New download contains newer virus definition and database to detect and clean most recent viruses.
To use this tool in removing Creeper, please follow this procedure.
1. Download Microsoft Safety Scanner from official web site. Click on the button below.
2. Save the file to a convenient location such as Desktop.
3. Once the download completes, browse the folder and double-click on the file msert.exe. Icon for this file looks like this.
4. If Windows prompts for a security warning and ask if you want to run the file, click on Run. For Windows Vista/7 users, you may right-click on the file and select Run as administrator from the selection.
5. On initial run, the tool will display End User License Agreement, please accept the terms and click Next. Continue on the process until you reach the Scan Type window.
6. Select on Full scan to entire the system and detect any presence of Creeper. Then, click Next button to begin the scan process. Scanning may take a while, please be patient.
7. Once Microsoft Safety Scanner finished on scanning the computer, it will display the result. If it finds presence of Creeper and other malware, the tool removes them automatically.
8. Click on Finish button to close the tool.
Recover Creeper Encrypted Files
Creeper Decryption Tool
At this time, there is no definite way to decrypt files encrypted by Creeper. We are waiting for decryption tool from various computer security developers. You will see update on this area as soon as Creeper decryptor was made available.Use ShadowExplorer to Recover Files
Recovering Creeper encrypted files using this tool may only be possible if the virus did not erased the Shadow Copies of files on your computer. Volume Shadow Service is a Windows feature and is a component of Windows Backup and System Restore. Backup data are kept automatically in the system after enabling System Restore. Therefore, you may never use this feature when System Restore not active on the computer.
1. Download the most recent version of ShadowExplorer from their official website. Click the button below.
2. Install this program on your computer. It should initialize after the installation process. You may also double-click the created icon to run ShadowExplorer.
3. On main interface, click on the Drive Path at upper left corner to list all Volume Shadow Copies kept on your computer.
4. Select preferred time and date you wish to restore. It is suggested to select the most recent copy before the Creeper infection.
5. Right-click on the folder you wish to restore. Then, click on Export.
6. ShadowExplorer will prompt for the new location of files to recover. Please specify the path where you want to save copies of your files.