Isearch.avg.com/search is not a virus the way many people have conceived. It is part of the AVG antivirus installation known as the AVG Secure Search. The fact that it comes bundled with the known antivirus product proves that it is clean and free from any hazard. Although, even it is safe, some computer users are annoyed with Isearch.avg.com/search. The way this custom search engine by AVG alters the home page is somehow exploitation to some users.
Robert La Nguyen
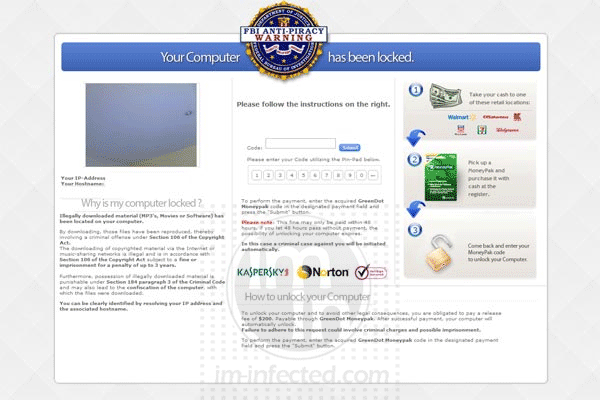
FBI Anti-Piracy Warning Malware
FBI Anti-Piracy Warning malware is a risky virus infection that can make your desktop unusable. In some instances, it is called as FBI Anti-Piracy Warning Greendot Moneypack because it is utilizing this payment scheme to steal money from computer users. Normally, the threat is known as �ransomware� because it will deny your access to your own PC until you pay for the unlock code.
Remove FindGala Hijacker
FindGala search hijacker and Toolbar is sorted as an adware that alters settings on the Internet browser. Anti-virus program will not detect FindGala as virus because it is not, but rather an add-on for Internet Explorer, Google Chrome, and Mozilla Firefox. User is often not aware of the installation. The adware usually comes with a program or tool that unknown web sites offer when you visit them. Programs you may download may be an Internet booster or multi-media player. Upon installing this software, FindGala is also being loaded without your knowledge.
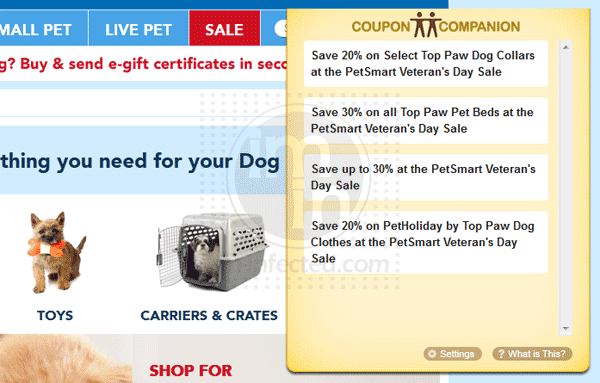
Remove Coupon Companion
Coupon Companion is an adware program that most users are deemed harmful. It presents corrupt way of promoting products on the Internet. It deprived your privacy while browsing the Internet because Coupon Companion monitors your activity and tries to display relevant ads. Normally, it offers huge savings for product within your interest.
Remove Coupondropdown Ads
Coupondropdown pop-up ads will appear on your browser if you have the add-on installed on the system. It is developed for product promotion and coupon deployment for savings on your online purchases. This is the reason why Coupondropdown pop-ups every time you are browsing the web.
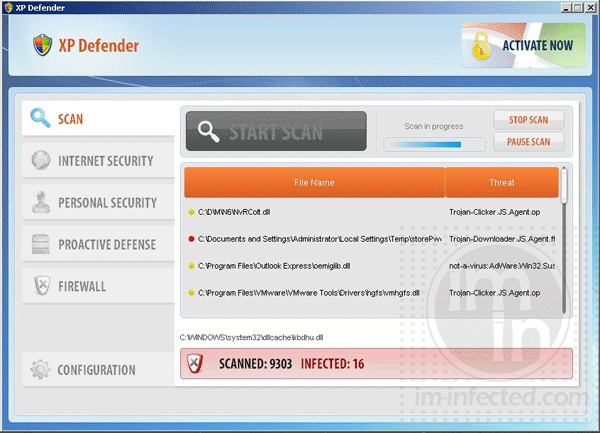
Uninstall XP Defender Virus
XP Defender virus is another form of rogue security tool. You may not want it inside the computer, but it will get there without your knowledge. Every computer user that is using the Internet without any caution is at risk of catching the XP Defender virus.
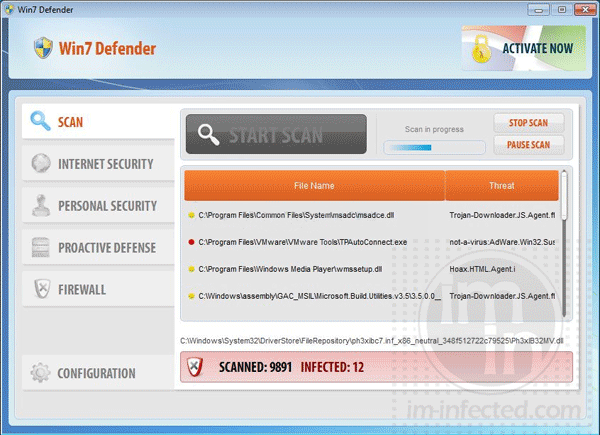
Remove Win7 Defender
Win7 Defender virus is one of the fake�security programs that put computer users into trouble. This rogue tool is part of a family that can identify the operating system. It is installed based on the gathered data to match the system. In this case, Win7 Defender infects Windows 7 computer.
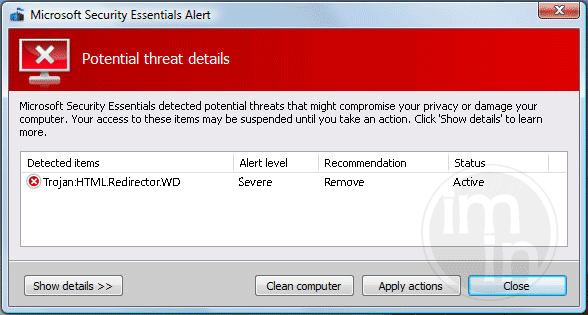
Remove Trojan HTML.Redirector.WD
Trojan HTML.Redirector.WD is a computer infection that affects mostly browsers like Internet Explorer, Mozilla Firefox, and Google Chrome. This Trojan is considered as malicious HTML web pages that try to exploits a weakness in your PC. Normally, Trojan HTML.Redirector.WD arrives when user pays a visit to compromised web sites. Threat may also be dropped on the system with another Trojan or virus infection. Free software downloads and file-sharing tools are seen to deploy copies of Trojan HTML.Redirector.WD.
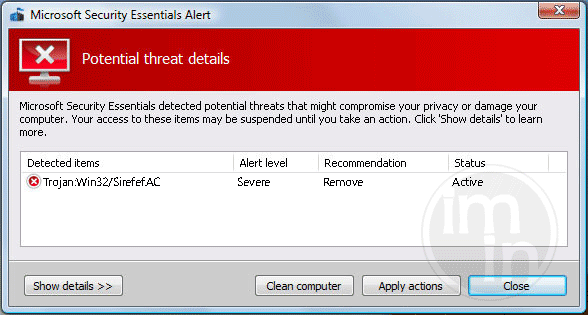
Remove Trojan:Win32/Sirefef.AC
Trojan:Win32/Sirefef.AC is a risky Trojan that may bring many changes on the infected computer. Once this threat is inside the system, it can freely alter settings on desktop, add other malware, and modify the registry to run harmful codes when Windows starts. Normally, main payload of Trojan:Win32/Sirefef.AC is to drop other threats including malware, viruses, and spyware. It is known to redirect Internet search to malicious web sites so that user instantly acquire other malware.
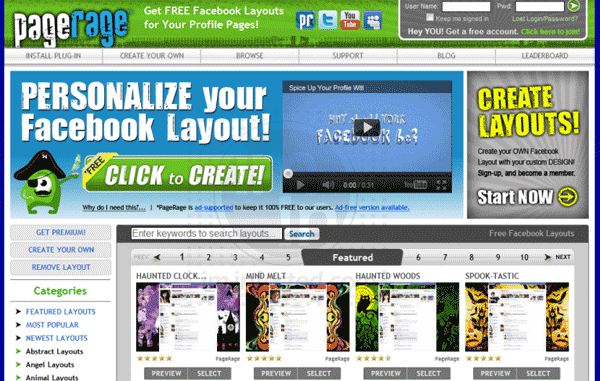
Remove PageRage Plug-in
Many computer users deemed PageRage as Facebook virus. In fact, PageRage is a tool that allows user to change or re-design profile pages. The fact that it allows user to have a user accounts and download the program indicates that manual intervention is required. User�s consent is sought before it can be loaded.