VirTool:Win32/Obfuscator.XZ is a malware that looks for system flaw in order to get into your PC. On other times, this Trojan misleads you to download software update, or deceive you to visit certain link. By any chance, once you make yourself believe to this nasty trick by VirTool:Win32/Obfuscator.XZ, chances are you will have added malware onto the computer.
How to remove Trojan.FakeAV!gen125
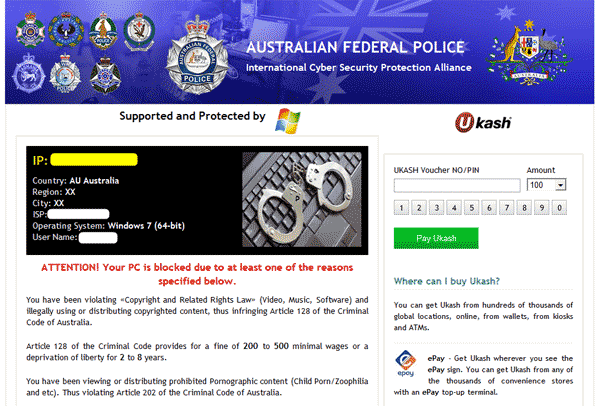
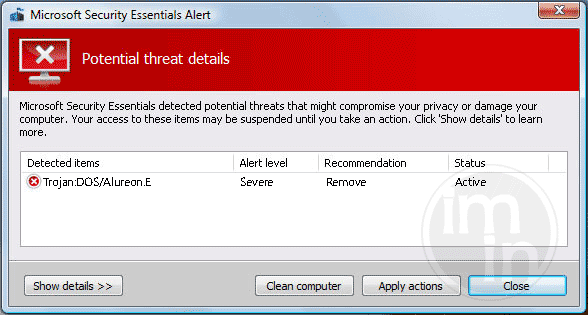
Trojan.FakeAV!gen125 is a detection for malware that attempts to drop and execute a copy of fake-antivirus program onto victim�s PC. To remove this threat, you must scan the system with legitimate anti-malware and anti-virus tools.