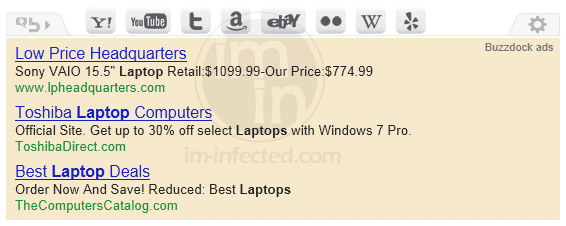
Many computer users wanted to uninstall�Buzzdock Ads because it is detected as an adware by some security program. This add-on for Internet browser was made possible with Addict-Thing plug-in. It is registered as Addict-Thing Class on Internet browser and performs as browser helper object (BHO). Unlike other unwanted add-ons, Buzzdock is not attuned to hijacking home page of the affected browser. It does not modify the search results and will never redirect it to unknown web sites.
Robert La Nguyen
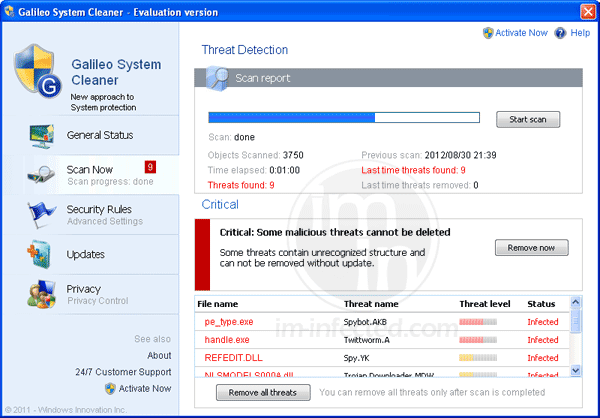
Remove Galileo System Cleaner
Galileo System Cleaner is another fake antivirus program that is part of Braviax family of malware. This is a computer hazard that does nothing but to show fake alerts and warnings. It attempts to force victims to pay for the Galileo System Cleaner registration key. In fact, it will detect non-existing threats and advise instant removal with the same tool.
Remove SVC:MBAMSwissArmy Rootkit
SVC:MBAMSwissArmy Rootkit will pop-up from an antivirus program if it detects a malicious service running on the system. The detection is for a legitimate file called mbamswissarmy.sys that is modified by a virus infection that causes the main program to fail. In addition, compromised file may be used by an attacker to launch other malware on the system. There are also other variants of Trojan hitting the same file in order to run a malware code every time the affected software is executed.
Remove Search us.com (start.search.us.com)
Search us.com is considered as browser hijacker because it modifies Internet browser without seeking for user�s approval. When it enters the computer, home page is replaced with a custom search bar bearing the address start.search.us.com. There are cases that it may display a simple view by pointing the homepage to search.us.com.
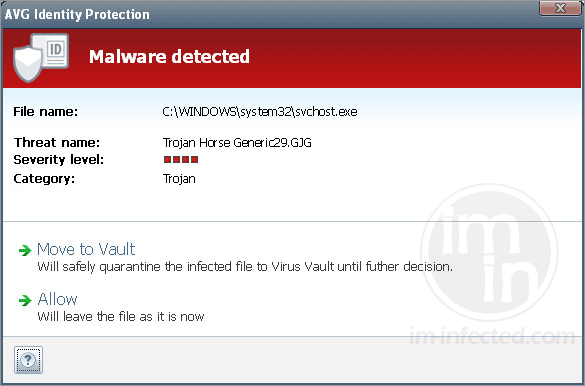
Remove Trojan Horse Generic29.GJG
Trojan Horse Generic29.GJG is a heuristic detection for a type of Trojan that shows the same characteristics. Most variants of this Trojan are capable of dropping other malware threats. A component known as backdoor may permit a remote attacker to enter the infected computer and do harmful actions. Trojan Horse Generic29.GJG modifies your system files and registry so that it loads whenever you start Windows.
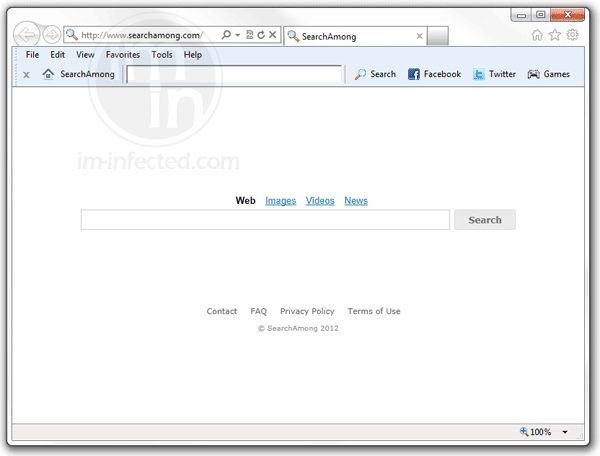
Remove Searchamong.com – SearchAmong Toolbar
Searchamong.com and SearchAmong Toolbar are part of adware program that loads on the computer upon installing unknown video player. The searchamong.com homepage overrides the current settings and replacing the default search box on affected computer�s browser. It is also noted that only Internet Explorer is affected by SearchAmong Toolbar add-on.
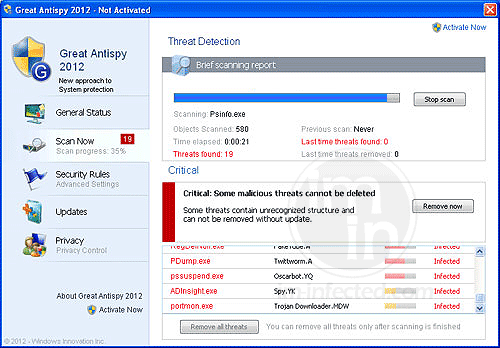
Remove Great Antispy 2012
Great Antispy 2012 mimics what real antivirus program does to be able to deceive computer users. It runs a scan each time you run Windows and provide a number of threats. Great Antispy 2012 also shows an array of fake warnings to make you think the PC is terribly infected with Trojans and viruses.
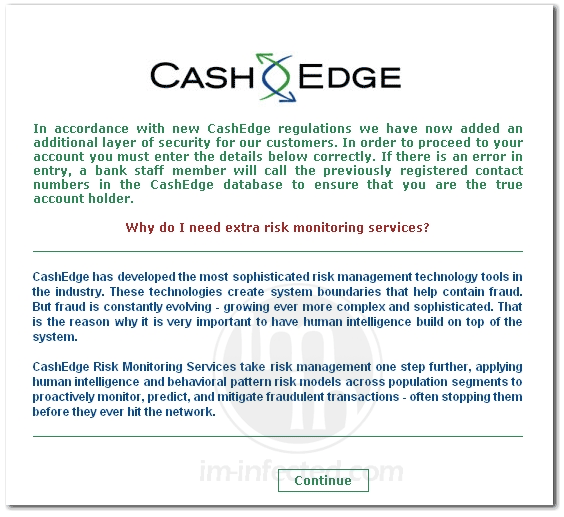
Remove Cash Edge Pop-up
Cash Edge Pop-up virus will appear on computers that is infected with a malware. Its purpose is mainly to steal personal and banking information from the victim. The message impersonates as a message from Cash Edge funds transfer system.
Uninstall Astrologic Registry Fixer
Astrologic Registry Fixer is a new type of fake system utility software made to deceive computer users. It spreads on the Internet via file-sharing servers, social networking sites, and spam email campaign. There are instances that Astrologic Registry Fixer is package with a fake Adobe Flash and Java Runtime update.
Remove Win32:DNSChanger-VJ [Trj]
Win32:DNSChanger-VJ [Trj] is a kind of computer Trojan that will alter infected computer�s Domain Name Server (DNS) settings to redirect Internet traffic to a different server. Typically, this redirect action is applied to hijack user�s web browser and point it to harmful or illegal web sites. It is observed that there are several purposes, but the main objective is to generate online profit for the attacker.